Security experts at Kaspersky Lab have discovered a modification of the mobile banking Trojan, Faketoken, which can encrypt user data. Kaspersky Lab has detected several thousand Faketoken installation packages capable of encrypting data, the earliest of which dates back to July 2016.
Disguised as various programs and games, including Adobe Flash Player, the modified Trojan can also steal credentials from more than 2000 Android financial applications.
To date, the modified Faketoken has claimed over 16,000 victims in 27 countries, with the most located in Russia, Ukraine, Germany and Thailand.
The newly added data-encryption capability is unusual in that most mobile ransomware focuses on blocking the device rather than the data, which is generally backed-up to the cloud.
In Faketoken’s case, the data – including documents and media files such as pictures and videos – is encrypted using AES symmetric encryption which can, in some cases, be decrypted by the victim without paying a ransom.
During the initial infection process, the Trojan demands administrator rights, permission to overlay other apps or to be a default SMS application – often leaving users with little or no choice but to comply. Among other things, these rights enable Faketoken to steal data: both directly, like contacts and files, and indirectly, through phishing pages.
The Trojan is designed for data theft on an international scale. Once all the necessary rights are in place, it downloads a database from its command and control server containing phrases in 77 languages for different device localisations.
These are used to create phishing messages to seize passwords from users’ Gmail accounts. The Trojan can also overlay the Google Play Store, presenting a phishing page to steal credit card details.
In fact, the Trojan can download a long list of applications for attack and even an HTML template page to generate phishing pages for the relevant apps. Kaspersky Lab researchers uncovered a list of 2249 financial applications.
Intriguingly, the modified Faketoken also tries to replace application shortcuts for social media networks, instant messengers and browsers with its own versions. The reason for this is unclear as the substitute icons lead to the same legitimate applications.
“The latest modification of the Faketoken mobile banking Trojan is interesting in that some of the new features appear to provide limited additional benefit for the attackers. That doesn’t mean we shouldn’t take them seriously. They may represent the groundwork for future developments, or reveal the ongoing innovation of an ever-evolving and successful malware family. In exposing the threat, we can neutralise it, and help to keep people, their devices and their data safe,” says Roman Unuchek, senior malware analyst at Kaspersky Lab.





![[IMG]](https://www.neowin.net/images/uploaded/shutterstock-businessman-looking-phone_story.jpg)
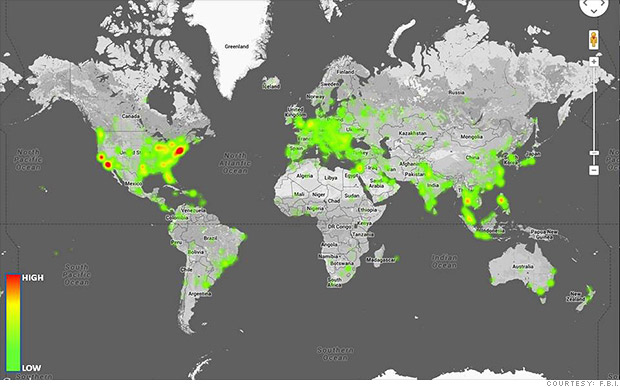 Officials say Blackshades was used to illegally access the computers of 700,000 victims around the world, as shown in this FBI heatmap.
Officials say Blackshades was used to illegally access the computers of 700,000 victims around the world, as shown in this FBI heatmap.
