MS Outlook Ad
What Microsoft Says
Microsoft Corporation once advertised, “We don’t go through your email to sell ads.” What Microsoft does instead is go through your email for everything else.
Microsoft is establishing a way for major Internet Service Providers to get away with accessing and using actual communications of customers while couching everything under “protection.” The violation goes way beyond the collection and storage of data while not even violating Microsoft’s own Privacy Policy or Terms of Service.
Since Microsoft and all the other big ISPs are now allowed by the Electronic Communications Privacy Act to read and disclose its customers communications (email, blogs, texts, chat), the law itself protects Microsoft and all ISPs and gives them a way out since they stand on the premise that the data belongs to them, so there is no expectation of privacy. Where does that leave you, the consumer, and what does it mean for journalists?
Recently Microsoft, without a court order, accessed the private emails and chat communications between one of its customers who was blogging with an ex MS employee. The employee did break the law,but Microsoft sidestepped legal process to gather the evidence on its own and then turn it over to authorities who proceeded to arrest the individual.
The current Administration has repeatedly assured us that the ISPs are innocently collecting and simply storing data in the name of national security’ in order to keep us all safe from terrorism. Not true since there is a little backdoor which allows Microsoft (because it can) to go in and search and read and use details of communications of its customers. In this case, Microsoft did just that by accessing the Hotmail account (which is now Outlook and owned by MS) of a customer because they wanted to use the information they found to go after an ex-employee.
It appears that ISPs get to invade customer communications because it is in THEIR best interest since the ECPA law was recently interpreted and changed to allow ISPs to get away with whatever they want to. What happened to due process? It is apparent that the bottom line is all that matters for the ISP.
In this particular case, Microsoft did not go to a judge or get a court order; and despite the public being assured that ISPs will not misuse the data they are ‘collecting and storing’, remember, they dont have to any more. Microsoft considers this information to belong to them in the first place.
After Microsoft came under fire for the incident, John Frank, Microsoft General Counsel, issued a statement that included magnificent double speak to convince us all that MS is only protecting their customers and justifying the action by saying his company “took extraordinary actions based on the specific circumstances” to “protect our customers and the security and integrity of our products.”
Oh yes, the action Microsoft took was indeed extraordinary.
Frank went on to justify the legal reasoning guiding Microsoft’s actions and explained how Microsoft adhered to its own terms of service as it was determined by its own investigation. Frank said that courts do not “issue orders authorizing someone to search themselves, since obviously no such order is needed,” basing his argument on Microsoft owns the data so they just don’t need a court order to go get whatever they want or target whomever they choose.
Frank added that Microsoft will not search customer email (and other communications) unless it would justify a court order if one were available. The fact is that if Microsoft does not follow legal procedures in the first place or attempt to get a court order, then of course there wont be one ‘available’ so he establishes the way out of following any due process.
Frank also made sure to tell us how Microsoft has had our backs and even has their very own internal process set up that is designed to protect customers from Microsoft deciding to grab emails and using the specific information. Part of the plan apparently involves an internal legal staff that operates independently from another internal department to jointly determine if a court order would otherwise be issued by a judge before they can go in (internally) and grab all your actual communications. Lots of ‘internal’ machinations go into the very internal determination. They even announced they will now follow extra steps and submit their evidence (noteevidence they already have collected) to an outside attorney to review.
One can safely assume Microsoft is paying this outside attorney as a consultant with a CDA in place, so of course this outside attorney is really an inside attorney on the side of MS, and this statement is simply double speak to make Microsoft look good. “Oh, we are hiring an outside attorney who used to be a former judge even! And he will help us determine if it’s okay for us to use emails and chat conversations of our customers before we decide to go use it.”
With the loss of Net Neutrality and the recent changes in the law that favor their bottom line, the ISPs like Microsoft, Google, Yahoo, can pretty much do what they want now and charge what they want. This is only the beginning of the double speak but there are still people who can see through. And, it’s not half way in and half way out, its never halfway when only the consumer is losing.
The incident should raise major red flags among bloggers and journalists who use Microsoft and other ISP services to communicate and do research, particularly when it comes to protection of sources.
for latest computer repair and online news.
Local and Online Virus removal and computer repairs anytime, anywhere
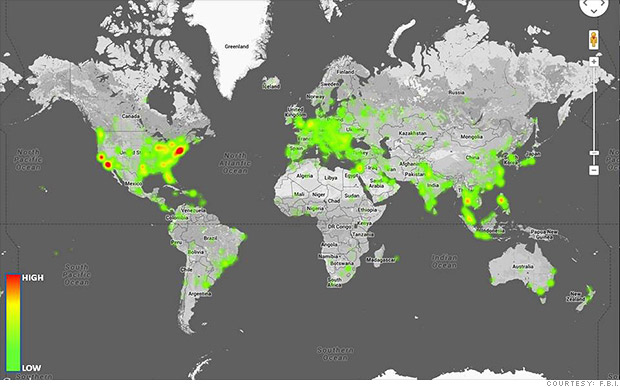 Officials say Blackshades was used to illegally access the computers of 700,000 victims around the world, as shown in this FBI heatmap.
Officials say Blackshades was used to illegally access the computers of 700,000 victims around the world, as shown in this FBI heatmap.