Once again, a new revelation showed the ugly side of the Government who are conducting Global Mass surveillance and previous documents leaked by the whistleblower Edward Snowden have defaced the US Intelligence Agency NSA, who were taking care of a number of projects like PRISM, XKeyscore, DROPOUTJEEP, and various others to carry out surveillance of millions of people.
Now, it has been revealed that the US National Security Agency (NSA) helped its British counterpart, the Government Communications Headquarters (GCHQ), to allegedly capture and store nude images and others from webcam chats of millions of unsuspecting Yahoo users, The Guardian reported.
Documents handed to the Guardian by the former NSA contractor Edward Snowden show that the GCHQ’s worked with the US intelligence agency NSA on a joint project dubbed as ‘Optic Nerve’. The project carried out a bulk surveillance program, under which they nabbed webcam images every five minutes from random Yahoo users’ video chats and stored them in a database.
The project didn’t target individual users; rather it targeted Yahoo webcam chats between 2008 and 2010. Indeed, the method of collection appears somewhat recklessly, and in just six months of period alone, the still images of about 1.8 million users were captured and stored in the government servers in 2008.
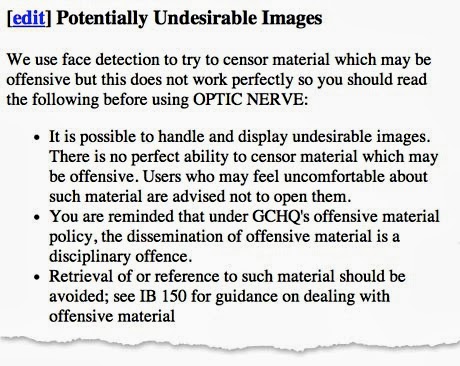
Instead of saving full videos, the program logged one image every five minutes from a user’s chat. The document says that between 3 and 11 percent of the images taken contain “undesirable nudity.”
One GCHQ document states, “It would appear that a surprising number of people use webcam conversations to show intimate parts of their body to the other person.”
The collected webcam information was stored in the NSA’s XKeyscore search tool, and the NSA research was used to build the tool which identified Yahoo’s webcam traffic, reads the report.
GCHQ webcam spying program, Optic Nerve, was still active in 2012, according to an internal GCHQ wiki page accessed that year.
Why Images??? It is known from the revealed documents that the images were collected by the government agency, so that the group could experiment with facial recognition.
“Face detection has the potential to aid selection of useful images for ‘mugshots’ or even for face recognition by assessing the angle of the face,” it reads. “The best images are ones where the person is facing the camera with their face upright.”
The GCHQ agency staffs were allowed to display “webcam images associated with similar Yahoo identifiers to your known target”, the document reads, also it states “Bulk surveillance of Yahoo users was begun” as “Yahoo webcam is known to be used by GCHQ targets.”
Not Surprising, because your knotty private webcam sex session you loved and enjoyed with your lover four years back was potentially pored over by the suits at GCHQ.
Yahoo has reacted furiously and denied any prior knowledge of the webcam interception program, and said that it had no awareness of or involvement with the GCHQ collection, describing the activity as “a whole new level of violation of our users’ privacy.”
And a GCHQ spokesman said in a statement, “It is a longstanding policy that we do not comment on intelligence matters. Furthermore, all of GCHQ’s work is carried out in accordance with a strict legal and policy framework which ensures that our activities are authorized, necessary and proportionate, and that there is rigorous oversight, including from the secretary of state, the interception and intelligence service commissioners and the Parliamentary Intelligence and Security Committee,” adding, “All our operational processes rigorously support this position.”
The NSA spokesperson declined to respond saying, “As we’ve said before, the National Security Agency does not ask its foreign partners to undertake any intelligence activity that the US government would be legally prohibited from undertaking it.”
This is how our privacy is getting ruined by the government intelligence officials that we all trust blindly.